-
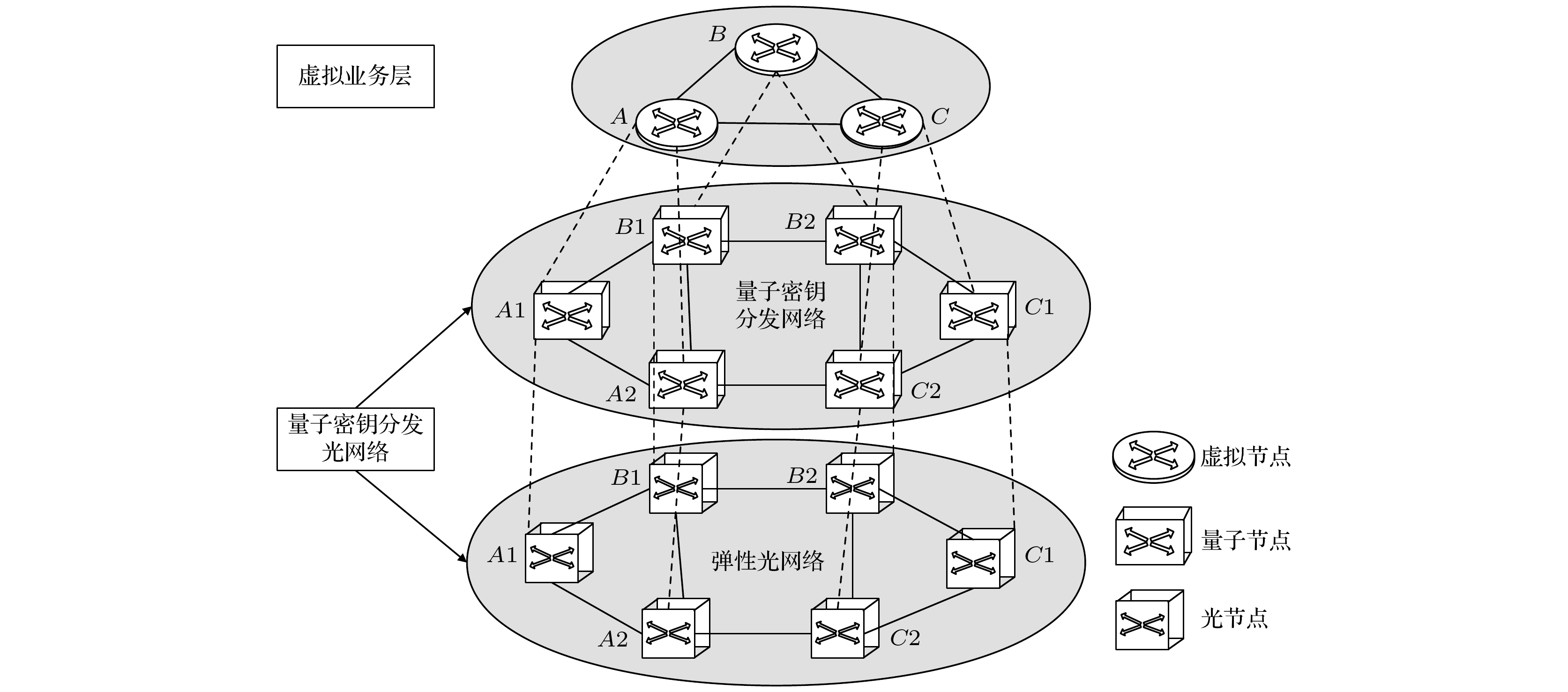
In the application research of large-scale quantum communication network, one generally realizes resource allocation by constructing virtual service network and mapping it to actual physical space. In this mapping process, some assumptions are often made to simplify the model. For example, the key resource in the physical topology is assumed to be a fixed value, that is, the actual physical conditions and the performance differences of key supply caused by different protocols are ignored. This assumption may lead the network to fail to run appropriately in practical applications. In order to solve the above problems, from the perspective of link mapping, this paper proposes an improved virtual service mapping model and virtual service mapping algorithm with the quantum key distribution optical network as the underlying network, which makes it closer to the actual application scenario. On the one hand, by increasing the constraints of geographical location, the range from virtual nodes to the mappable physical nodes is reasonably restricted. On the other hand, from the perspective of hardware cost and actual key generation rate, the cost performance evaluation index is proposed to allocate and manage resources. In addition, by combining three mainstream quantum key distribution protocols (BB84, measurement-device-independent, and twin-field), we construct a universal virtual service mapping model in the quantum key distribution optical network, and realize the recommendation of the optimal protocol and the optimal allocation and management of resources.
-
Keywords:
- optimal allocation of resources /
- quantum key distribution /
- virtual service embedding /
- cost performance
[1] Lin R P, Luo S, Zhou J W, Wang S, Cai A L, Zhong W D, Moshe Z 2018 J. Lightwave Technol. 36 3551
 Google Scholar
Google Scholar
[2] Jiang H H, Wang Y X, Gong L, Zhu Z Q 2015 J. Opt. Commun. Netw. 7 1160
 Google Scholar
Google Scholar
[3] Gong L, Zhu Z 2013 J. Lightwave Technol. 32 450
 Google Scholar
Google Scholar
[4] Jarray A, Karmouch A 2014 IEEE/ACM Trans. Netw. 23 1012
 Google Scholar
Google Scholar
[5] Botero J F, Hesselbach X, Fischer A, Hermann D M 2012 Telecommun. Syst. 51 273
 Google Scholar
Google Scholar
[6] 王妍 2020 硕士学位论文(北京: 北京邮电大学)
Wang Y 2020 M. S. Dessertation (Beijing: Beijing University of Posts and Telecommunications ) (in Chinese)
[7] Zeng P, Zhou H Y, Wu W J, Ma X F 2022 Nat. Commun. 13 1
 Google Scholar
Google Scholar
[8] Zhou X Y, Zhang C H, Zhang C M, Wang Q 2019 Phys. Rev. A 99 062316
 Google Scholar
Google Scholar
[9] Mao Y Q, Wang B X, Zhao C X, Wang G Q, Wang R C, Wang H H, Zhou F, Nie J M, Chen Q, Zhao Y, Zhang Q, Zhang J, Chen T Y, Pan J W 2018 Opt. Express 26 6010
 Google Scholar
Google Scholar
[10] 王鹏辉, 张宁, 肖明明 2019 计算机工程与应用 55 106
 Google Scholar
Google Scholar
Wang P H, Zhang N, Xiao M M 2019 Comput. Eng. Appl. 55 106
 Google Scholar
Google Scholar
[11] Gottesman D, Lo H K, Lutkenhaus N, Preskill J 2004 Quantum Inf. Comput. 4 325
 Google Scholar
Google Scholar
[12] 朱凤丹 2016 硕士学位论文 (南京: 南京邮电大学)
Zhu F D 2016 M. S. Thesis (Nanjing: Nanjing University of Posts and Telecommunications) (in Chinese)
[13] Zhou Y H, Yu Z W, Wang X B 2016 Phys. Rev. A 93 042324
 Google Scholar
Google Scholar
[14] Xu H, Yu Z W, Jiang C, Hu X L, Wang X B 2020 Phys. Rev. A 101 042330
 Google Scholar
Google Scholar
[15] Cao Y, Zhao Y L, Wang Q, Zhang J, Ng S X, Hanzo L 2022 IEEE Commun. Surv. Tut. 24 839
 Google Scholar
Google Scholar
[16] 赵礼峰, 黄奕雯 2017 计算机技术与发展 27 98
 Google Scholar
Google Scholar
Zhao L F, Huang Y W 2017 Comput. Technol. Dev. 27 98
 Google Scholar
Google Scholar
[17] Xu F, Xu H, Lo H K 2014 Phys. Rev. A. 89 052333
 Google Scholar
Google Scholar
[18] Yin H L, Chen T Y, Yu Z W, Liu H, You L X, Zhou Y H, Chen S J, Mao M Q, Huang M Q, Zhang W J, Chen H, Li M J, Nolan D, Zhou F, Jiang X, Wang Z, Zhang Q, Wang X B, Pan J W 2016 Phys. Rev. Lett. 117 190501
 Google Scholar
Google Scholar
[19] Liu Y, Yu Z W, Zhang W J, Guan J Y, Chen J P, Zhang C, Hu X L, Li H, Jiang C, Lin J, Chen T Y, You L X, Wang Z, Wang X B, Zhang Q, Pan J W 2019 Phys. Rev. Lett. 123 100505
 Google Scholar
Google Scholar
-
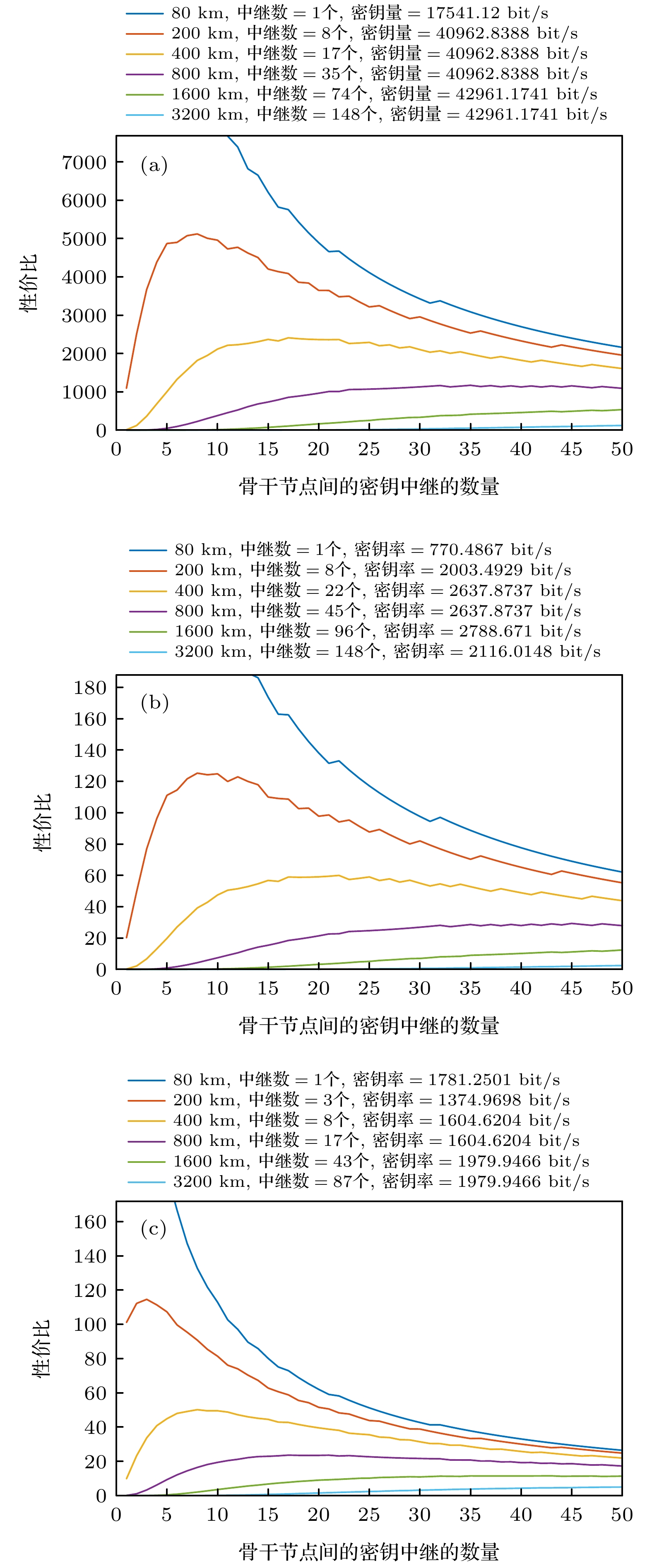
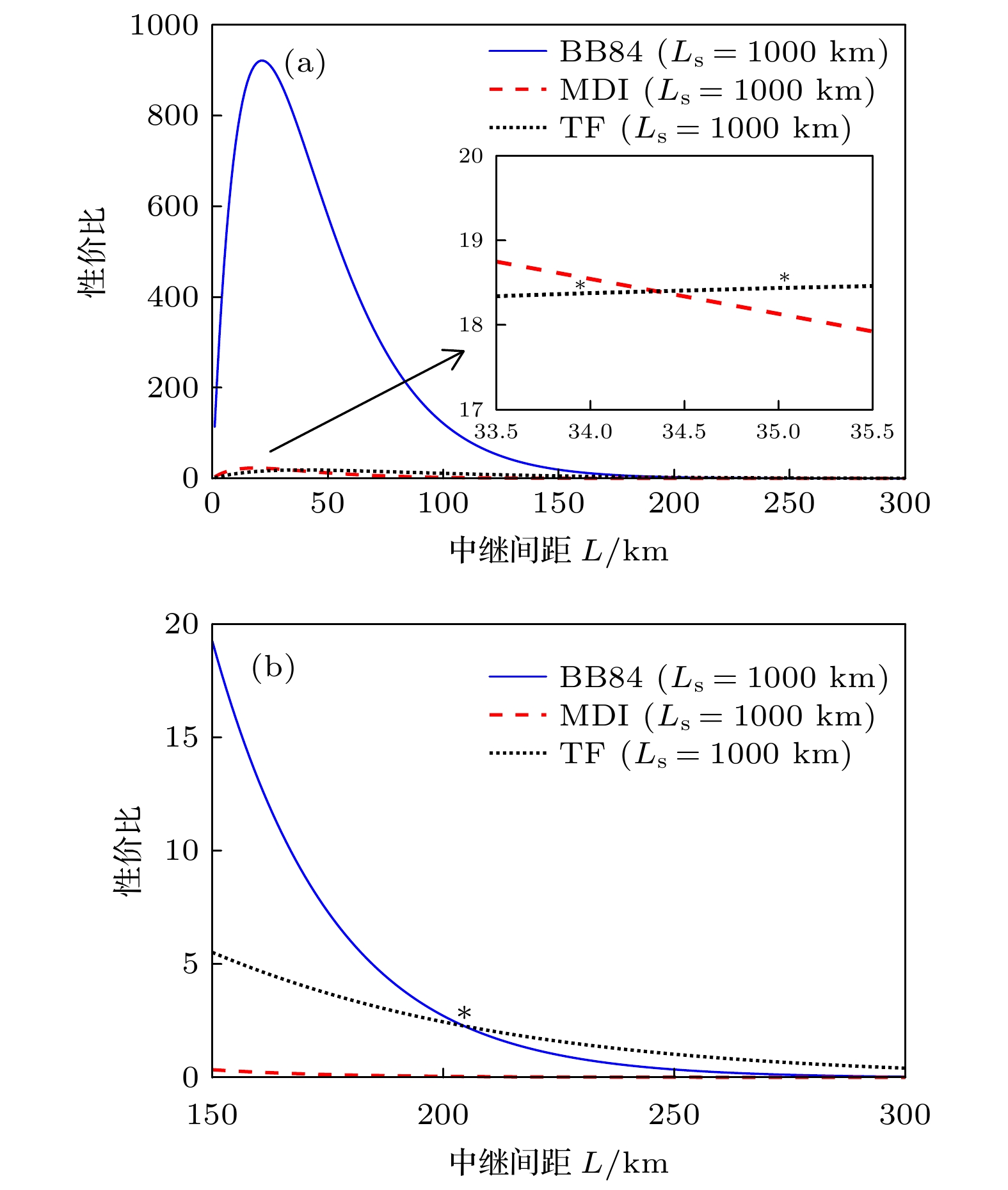
图 6 (a)采用BB84协议时不同距离下中继数量与性价比关系图; (b)采用MDI协议时不同距离下中继数量与性价比关系图; (c)采用TF协议时不同距离下中继数量与性价比关系图
Figure 6. (a) Plot of relay number and cost performance at different distances with BB84 protocol; (b) plot of relay number and cost performance at different distances with measurement-device-independent protocol; (c) plot of relay number and cost performance at different distances with two-field protocol.
表 1 虚拟节点可映射范围求解算法
Table 1. Mapping range solving algorithm for the virtual nodes.
输入 虚拟节点$ {v}_{i}^{\rm{v}} $, 物理节点$ {v}_{i}^{\rm{p}} $, 物理网络
${G}^{\rm{p} }\left({V}^{\rm{p} },\; {L}^{\rm{p} },\; {BW}^{\rm{p} },\; {K}^{\rm{p} }\right)$输出 虚拟节点${v}_{i}^{{\rm{v}}}$可映射的物理节点范围${D}_{i}^{{\rm{v}}}$ 1 For 每个虚拟节点$ {v}_{i}^{\rm{v}} $ do 2 随机生成一个相应的物理节点$ {v}_{i}^{\rm{p}} $ 3 End for 4 For 每个物理节点$ {v}_{i}^{\rm{p}} $ do 5 根据USNET网络拓扑图得出与每个物理节点直
接相连的节点6 将物理节点$ {v}_{i}^{\rm{p}} $和与其直接相连的节点, 记为$ {D}_{i}^{\rm{v}} $ 7 End for 8 每个虚拟节点$ {v}_{i}^{\rm{v}} $可映射的物理节点范围为$ {D}_{i}^{\rm{v}} $ 表 2 每个虚拟节点可映射的物理节点范围
Table 2. The range of physical nodes that can be mapped to each virtual node.
随机生成物理节点 可映射物理节点范围 随机生成物理节点 可映射物理节点范围 随机生成物理节点 可映射物理节点范围 1 1, 2, 6 9 9, 6, 7, 10, 11, 12 17 17, 13, 16, 18, 22, 23 2 2, 1, 3, 6 10 10, 8, 9, 13, 14 18 18, 14, 17, 24 3 3, 2, 4, 5, 7 11 11, 6, 9, 12, 15, 19 19 19, 11, 20 4 4, 3, 5, 7 12 12, 9, 11, 13, 16 20 20, 15, 19, 21 5 5, 3, 4, 8 13 13, 10, 12, 14, 17 21 21, 16, 20, 22 6 6, 1, 2, 7, 9, 11 14 14, 10, 13, 18 22 22, 16, 17, 21, 23 7 7, 3, 4, 6, 8, 9 15 15, 11, 16, 20 23 23, 17, 22, 24 8 8, 5, 7, 10 16 16, 12, 15, 17, 21, 22 24 24, 18, 23 表 3 仿真参数
Table 3. Simulation parameters
α/(dB·km–1) $ {e}_{\rm{d}\rm{e}\rm{t}\rm{e}\rm{c}\rm{t}\rm{o}\rm{r}} $ $ {Y}_{0} $ $ {\eta }_{\rm{B}\rm{o}\rm{b}} $ $ f/\rm{M}\rm{H}\rm{z} $ 0.2 0.015 $ {10}^{-8} $ 0.5 2 表 4 仿真参数
Table 4. Simulation parameters.
名称 值 名称 值 物理节点数量 24个 物理链路数量 43条 链路频谱数量 386个 每条虚拟链路带宽需求 {5, 6, 7, 8, 9}个 虚拟节点数量 {2, 3, 4}个 每条虚拟链路密钥需求 {2000, 2400, 2800, 3200, 3600}bit -
[1] Lin R P, Luo S, Zhou J W, Wang S, Cai A L, Zhong W D, Moshe Z 2018 J. Lightwave Technol. 36 3551
 Google Scholar
Google Scholar
[2] Jiang H H, Wang Y X, Gong L, Zhu Z Q 2015 J. Opt. Commun. Netw. 7 1160
 Google Scholar
Google Scholar
[3] Gong L, Zhu Z 2013 J. Lightwave Technol. 32 450
 Google Scholar
Google Scholar
[4] Jarray A, Karmouch A 2014 IEEE/ACM Trans. Netw. 23 1012
 Google Scholar
Google Scholar
[5] Botero J F, Hesselbach X, Fischer A, Hermann D M 2012 Telecommun. Syst. 51 273
 Google Scholar
Google Scholar
[6] 王妍 2020 硕士学位论文(北京: 北京邮电大学)
Wang Y 2020 M. S. Dessertation (Beijing: Beijing University of Posts and Telecommunications ) (in Chinese)
[7] Zeng P, Zhou H Y, Wu W J, Ma X F 2022 Nat. Commun. 13 1
 Google Scholar
Google Scholar
[8] Zhou X Y, Zhang C H, Zhang C M, Wang Q 2019 Phys. Rev. A 99 062316
 Google Scholar
Google Scholar
[9] Mao Y Q, Wang B X, Zhao C X, Wang G Q, Wang R C, Wang H H, Zhou F, Nie J M, Chen Q, Zhao Y, Zhang Q, Zhang J, Chen T Y, Pan J W 2018 Opt. Express 26 6010
 Google Scholar
Google Scholar
[10] 王鹏辉, 张宁, 肖明明 2019 计算机工程与应用 55 106
 Google Scholar
Google Scholar
Wang P H, Zhang N, Xiao M M 2019 Comput. Eng. Appl. 55 106
 Google Scholar
Google Scholar
[11] Gottesman D, Lo H K, Lutkenhaus N, Preskill J 2004 Quantum Inf. Comput. 4 325
 Google Scholar
Google Scholar
[12] 朱凤丹 2016 硕士学位论文 (南京: 南京邮电大学)
Zhu F D 2016 M. S. Thesis (Nanjing: Nanjing University of Posts and Telecommunications) (in Chinese)
[13] Zhou Y H, Yu Z W, Wang X B 2016 Phys. Rev. A 93 042324
 Google Scholar
Google Scholar
[14] Xu H, Yu Z W, Jiang C, Hu X L, Wang X B 2020 Phys. Rev. A 101 042330
 Google Scholar
Google Scholar
[15] Cao Y, Zhao Y L, Wang Q, Zhang J, Ng S X, Hanzo L 2022 IEEE Commun. Surv. Tut. 24 839
 Google Scholar
Google Scholar
[16] 赵礼峰, 黄奕雯 2017 计算机技术与发展 27 98
 Google Scholar
Google Scholar
Zhao L F, Huang Y W 2017 Comput. Technol. Dev. 27 98
 Google Scholar
Google Scholar
[17] Xu F, Xu H, Lo H K 2014 Phys. Rev. A. 89 052333
 Google Scholar
Google Scholar
[18] Yin H L, Chen T Y, Yu Z W, Liu H, You L X, Zhou Y H, Chen S J, Mao M Q, Huang M Q, Zhang W J, Chen H, Li M J, Nolan D, Zhou F, Jiang X, Wang Z, Zhang Q, Wang X B, Pan J W 2016 Phys. Rev. Lett. 117 190501
 Google Scholar
Google Scholar
[19] Liu Y, Yu Z W, Zhang W J, Guan J Y, Chen J P, Zhang C, Hu X L, Li H, Jiang C, Lin J, Chen T Y, You L X, Wang Z, Wang X B, Zhang Q, Pan J W 2019 Phys. Rev. Lett. 123 100505
 Google Scholar
Google Scholar
Catalog
Metrics
- Abstract views: 8430
- PDF Downloads: 106
- Cited By: 0














 DownLoad:
DownLoad: