-
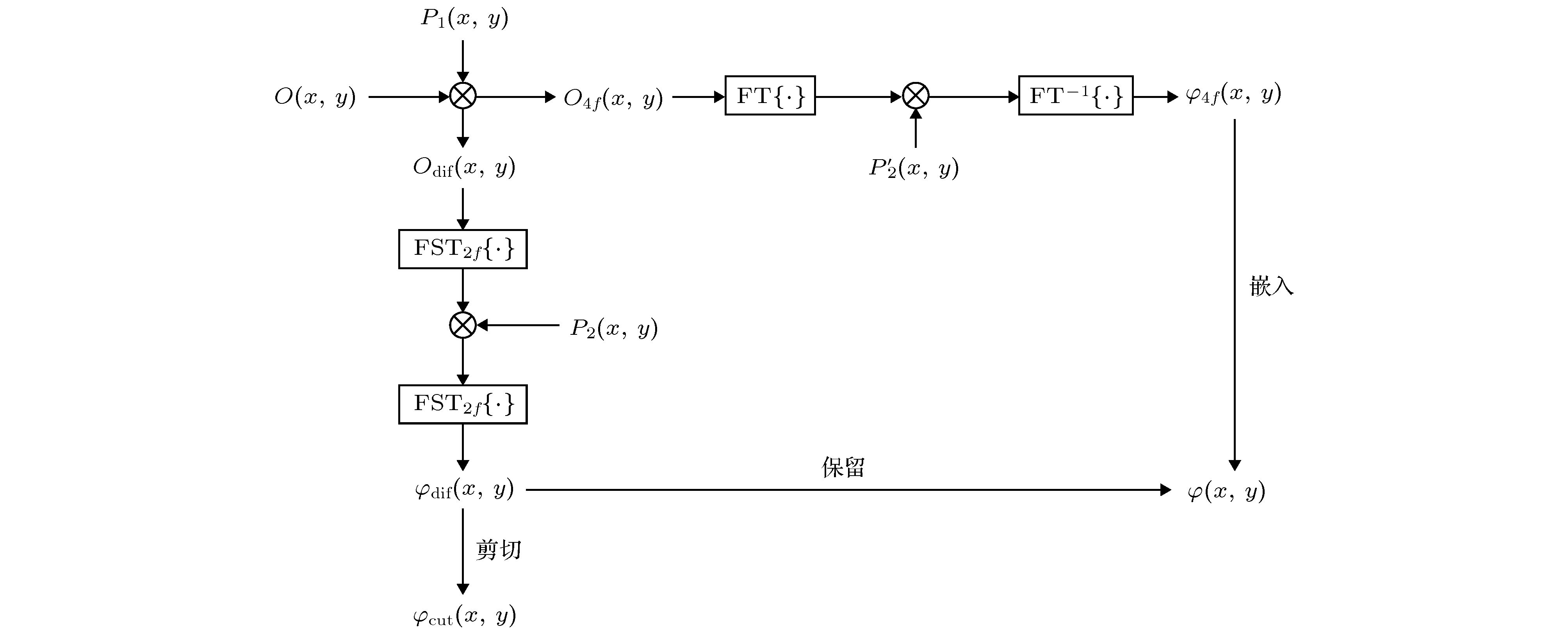
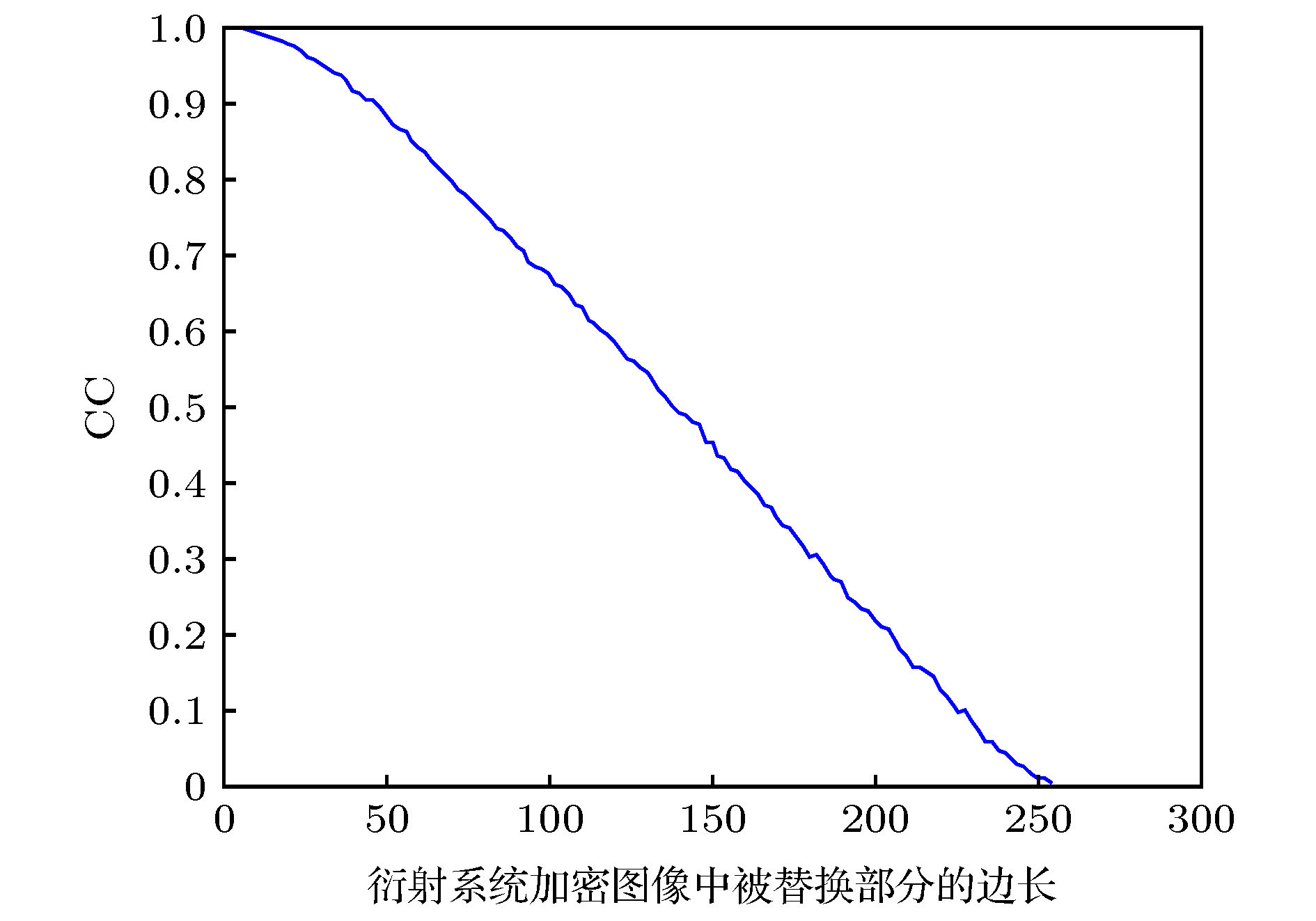
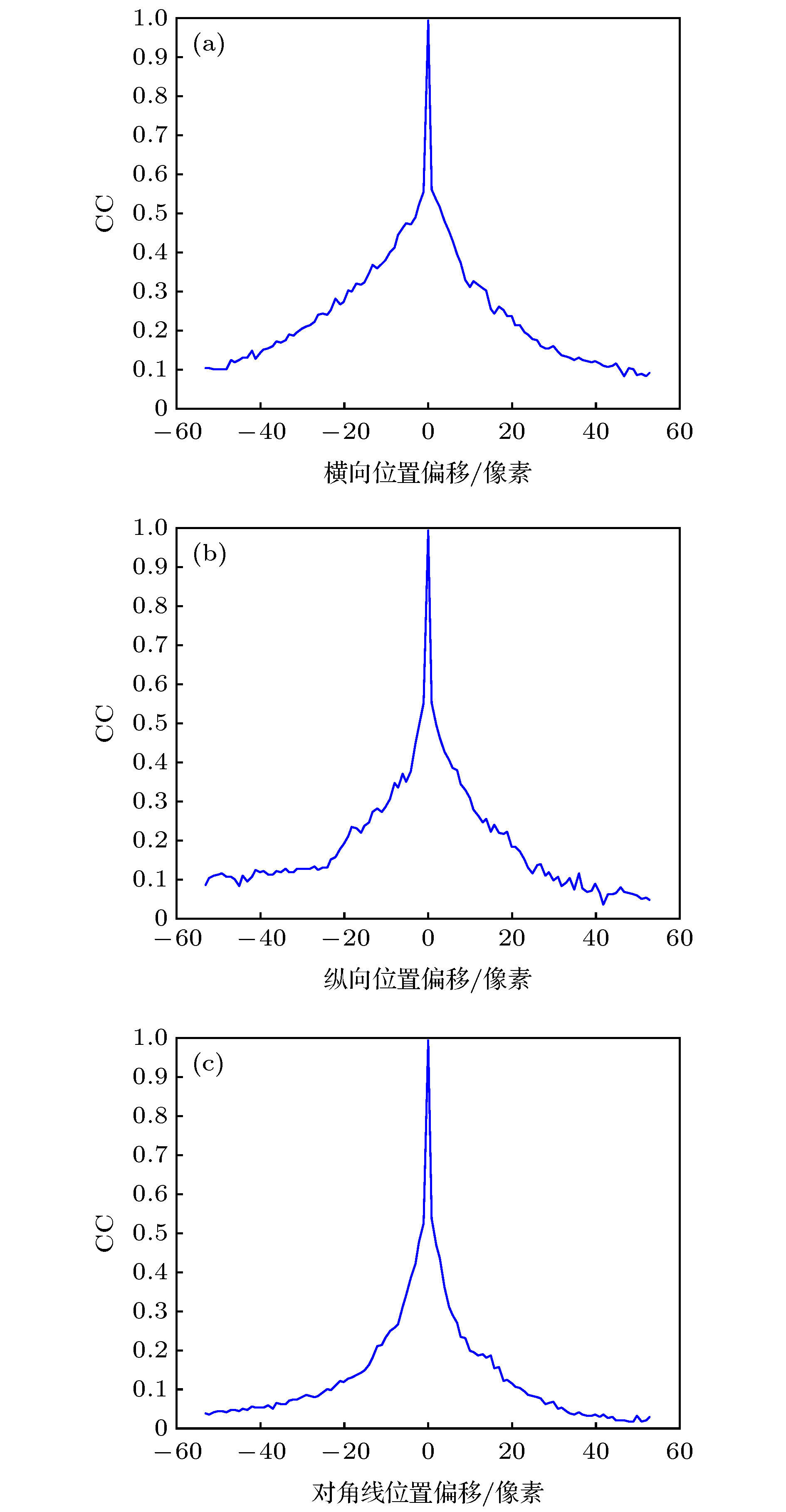
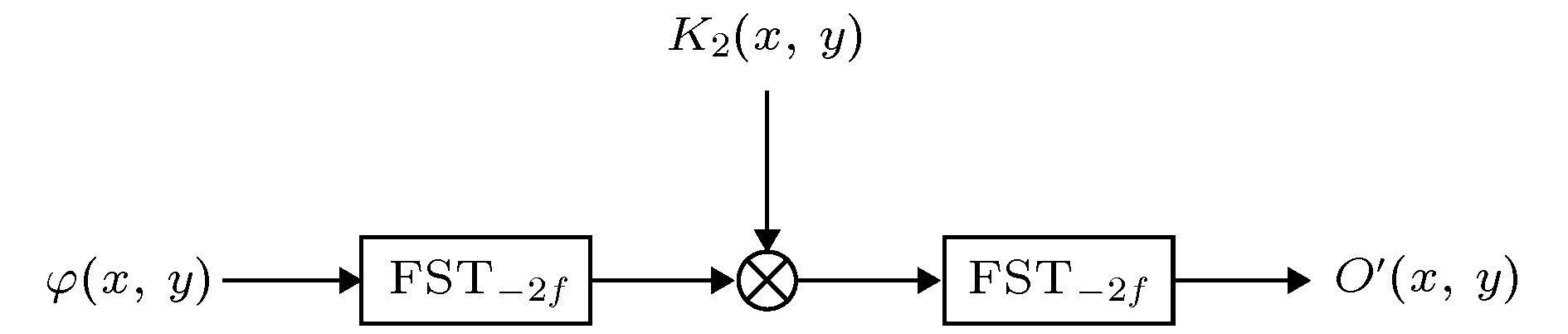
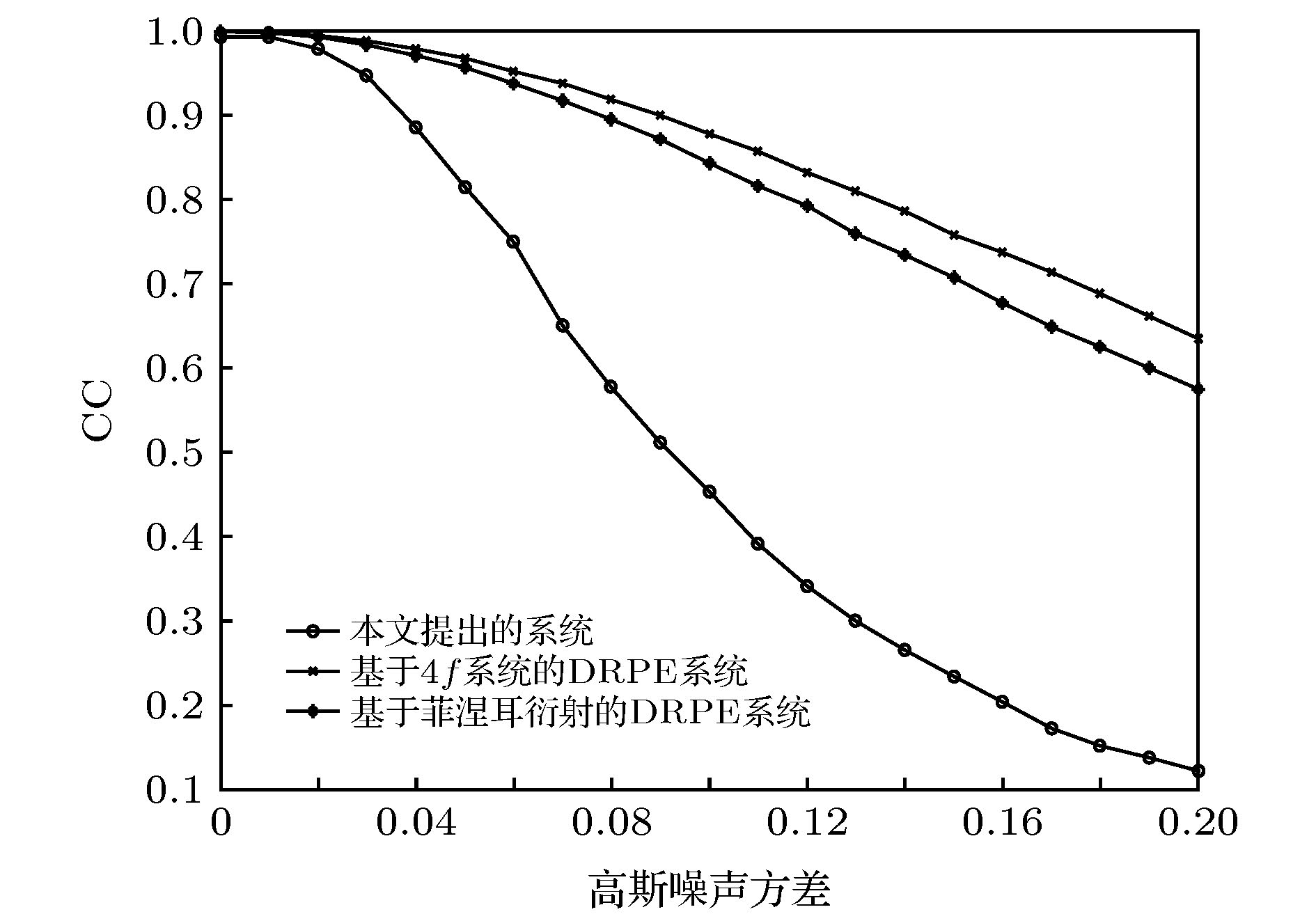
针对目前图像的选择性加密无法通过光学结构实现的问题, 通过光学设计方法, 将基于4f系统的双随机相位编码技术和基于衍射系统的双随机相位编码技术相结合, 提出了一种基于双随机相位编码的局部混合光学加密系统. 在该系统中, 原始图像被分为重要信息和非重要信息, 重要信息在4f系统中进行加密, 非重要信息在衍射系统中进行加密, 用4f系统密文替换掉衍射系统密文中的一部分, 得到最终的加密图像. 解密为加密的逆过程, 将4f系统密文从最终密文中剪切出来后, 用其还原出衍射系统密文中被替换掉的信息, 从而得到完整的衍射系统密文, 两个密文分别经过各自对应系统的逆过程后完成解密. 该方法实现了通过光学结构对图像进行选择性加密, 安全有效, 具有良好的鲁棒性. 通过仿真实验验证了该方法的有效性, 利用相关系数对该方法的加密和解密效果进行了评估, 验证了该方法的安全性.Most of the existing selective encryption schemes are based on image processing and cannot be realized by optical structures, so their practicality is limited. Combining the optical design, a local hybrid optical encryption system based on double random phase encoding is proposed. The system proposed in this paper possesses a common aperture and dual optical path structure, which is widely used in optical design and can effectively improve the practicality of optical encryption system. First, important information and non-important information in the original image are separated by a selective beam splitter. Then light waves carrying important information enter into the 4f system for encryption, and light waves carrying non-important information enter into the diffraction system for encryption. Finally, part of the diffraction system ciphertext is replaced with 4f system ciphertext to obtain the final encrypted image. Decryption is the reverse process of encryption. First, the 4f system ciphertext is cut out from the final ciphertext. Then the 4f system ciphertext is used to restore the information replaced in the diffraction system ciphertext, thereby obtaining the complete diffraction system ciphertext. Finally, the two ciphertexts go through the reverse process of their respective systems to complete the decryption. By comparing the statistical characteristics and mean square error of the original image and the encrypted image, the effectiveness of the proposed system's encryption process is proved. By analyzing the peak signal-to-noise ratio of the original image and the decrypted image, the effectiveness of the proposed system's decryption process is proved. The sensitivity of each key of the system is analyzed to prove the security of the system. Especially the system is highly sensitive to selective encryption key, which proves the effectiveness and security of the proposed system for selective encryption. Through simulation, it is verified that the proposed system is very resistant to diffraction attacks. Even if he can obtain all the diffraction keys, the attacker still cannot obtain the selectively encrypted information. Finally, through simulation, it is verified that the proposed system has good noise resistance and crop resistance, and high robustness as well. The proposed system can realize the selective encryption through optical structure, which is safe, effective and highly robust, and thus improving the practicality of selective optical encryption system.
[1] Refregier P, Javidi B 1995 Opt. Lett. 20 767
 Google Scholar
Google Scholar
[2] Tajahuerce E, Javidi B 2001 Appl. Opt. 39 6595
[3] Javidi B 2000 Opt. Eng. 39 2031
 Google Scholar
Google Scholar
[4] Wu C H, Chang J, Quan C G, Zhang Y J 2020 Opt. Commun. 462 125347
 Google Scholar
Google Scholar
[5] Yu H H, Chang J, Liu X, Wu C H, He Y F, Zhang Y J 2017 Opt. Express 25 8860
 Google Scholar
Google Scholar
[6] Sui L S, Gao B 2013 Opt. Laser Technol. 48 117
 Google Scholar
Google Scholar
[7] He W Q, Peng X, Meng X F 2012 J. Opt. 14 075401
 Google Scholar
Google Scholar
[8] Unnikrishnan G, Joseph J, Singh K 2000 Opt. Lett. 25 887
 Google Scholar
Google Scholar
[9] Situ G H, Zhang J J 2004 Opt. Lett. 29 1854
[10] Unnikrishnan G 2000 Opt. Eng. 39 2853
 Google Scholar
Google Scholar
[11] 彭翔, 汤红乔, 田劲东 2007 物理学报 56 2629
 Google Scholar
Google Scholar
Peng X, Tang H Q, Tian J D 2007 Acta Phys. Sin. 56 2629
 Google Scholar
Google Scholar
[12] Peng X, Zhang P, Wei H Z, Yu B 2006 Opt. Lett. 31 1044
 Google Scholar
Google Scholar
[13] Wu C H, Chang J, Xu X X, Zhang Y J 2019 Opt. Commun. 450 87
 Google Scholar
Google Scholar
[14] Shi Y S, Situ G H, Zhang J J 2007 Opt. Lett. 32 1914
 Google Scholar
Google Scholar
[15] QinY, GongQ, WangZ P 2014 Opt. Express 22 21790
 Google Scholar
Google Scholar
[16] Sun M J, Shi J H, Li H, Zeng G H 2013 Opt. Express 21 19395
 Google Scholar
Google Scholar
[17] Chen L F, Chang G J, He B Y, Mao H D, Zhao D M 2017 Opt. Laser Eng. 88 221
 Google Scholar
Google Scholar
[18] Xiang T, Wong K W, Liao X 2007 Chaos (Woodbury, N.Y.) 17 23115
 Google Scholar
Google Scholar
[19] Taneja N, Raman B, Gupta I 2011 Aeu Int. J. Electron. Commun. 65 338
 Google Scholar
Google Scholar
[20] Bhatnagar G, Wu Q M J 2012 Digit. Signal Process. 22 648
 Google Scholar
Google Scholar
[21] 孔德照, 沈学举, 林超, 杨鹏, 潘宇 2013 光学仪器 35 17
 Google Scholar
Google Scholar
Kong D Z, Shen X J, Lin C, Yang P, Pan Y 2013 Opt. Instr. 35 17
 Google Scholar
Google Scholar
[22] 肖宁, 李爱军 2017 应用光学 38 406
Xiao N, Li A J 2017 J. Appl. Opt. 38 406
[23] 彭翔, 位恒政, 张鹏 2007 物理学报 56 3924
 Google Scholar
Google Scholar
Peng X, Wei Z H, Zhang P 2007 Acta Phys. Sin. 56 3924
 Google Scholar
Google Scholar
[24] 史祎诗, 司徒国海, 张静娟 2008 光子学报 37 1779
Shi Y S, Situ G H, Zhang J J 2008 Acta Photon. Sin. 37 1779
-
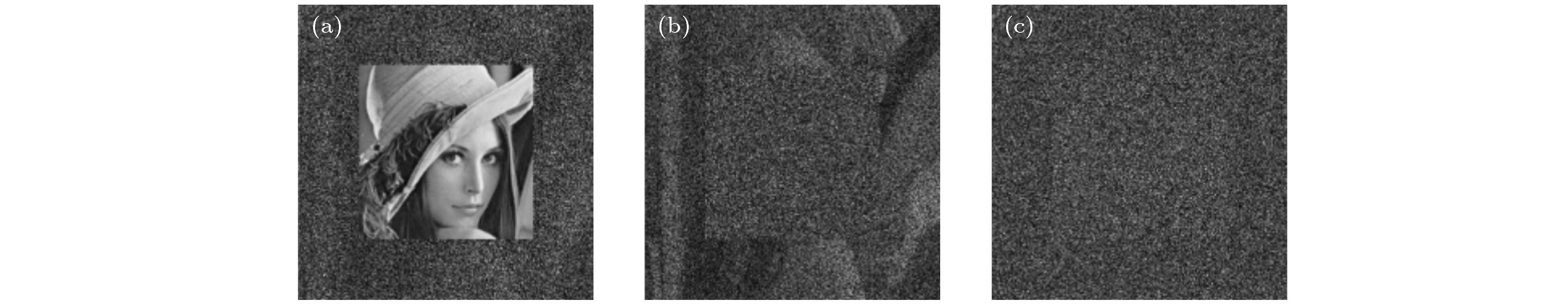
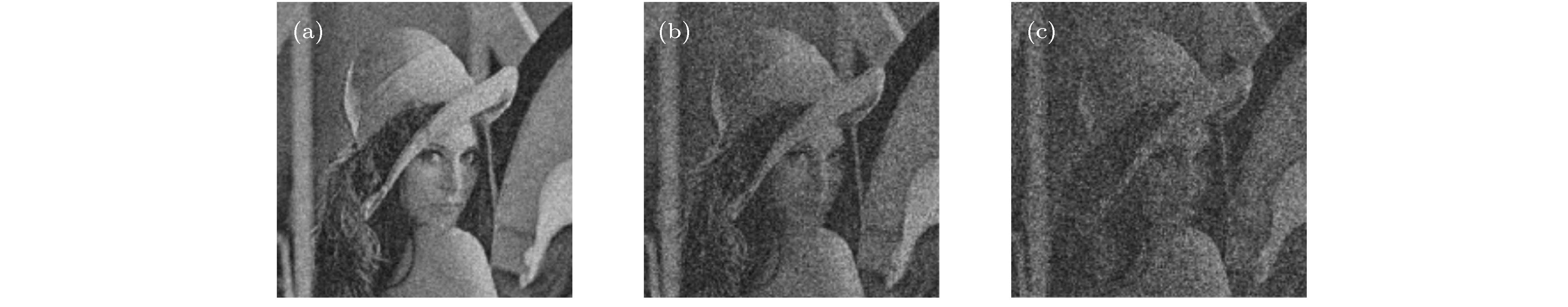
图 7 相位函数
${K_2}\left( {x, y} \right)$ 错误时的解密图像 (a)${K_2}\left( {x, y} \right)$ 中$K_2'(x, y)$ 正确, 其他相位信息错误; (b)${K_2}\left( {x, y} \right)$ 中$K_2'(x, y)$ 错误, 其他相位信息正确; (c)${K_2}\left( {x, y} \right)$ 完全错误Fig. 7. Decrypted image with wrong phase function
${K_2}\left( {x, y} \right)$ : (a)$K_2'(x, y)$ is correct in${K_2}\left( {x, y} \right)$ , other phase information is wrong; (b)$K_2'(x, y)$ is wrong in${K_2}\left( {x, y} \right)$ , other phase information is correct; (c)${K_2}\left( {x, y} \right)$ completely wrong.图 8 图像剪切的尺寸不同对应的解密图像(剪切图像正确尺寸为150 × 150) (a) 50 × 50, CC = 0.2272; (b) 150 × 150, CC = 0.9934; (c) 250 × 250, CC = 0.0056
Fig. 8. Decrypted images for different cropped image sizes (the correct size of the cropped image is 150 × 150): (a) 50 × 50, CC = 0.2272; (b) 150 × 150, CC = 0.9934; (c) 250 × 250, CC = 0.0056.
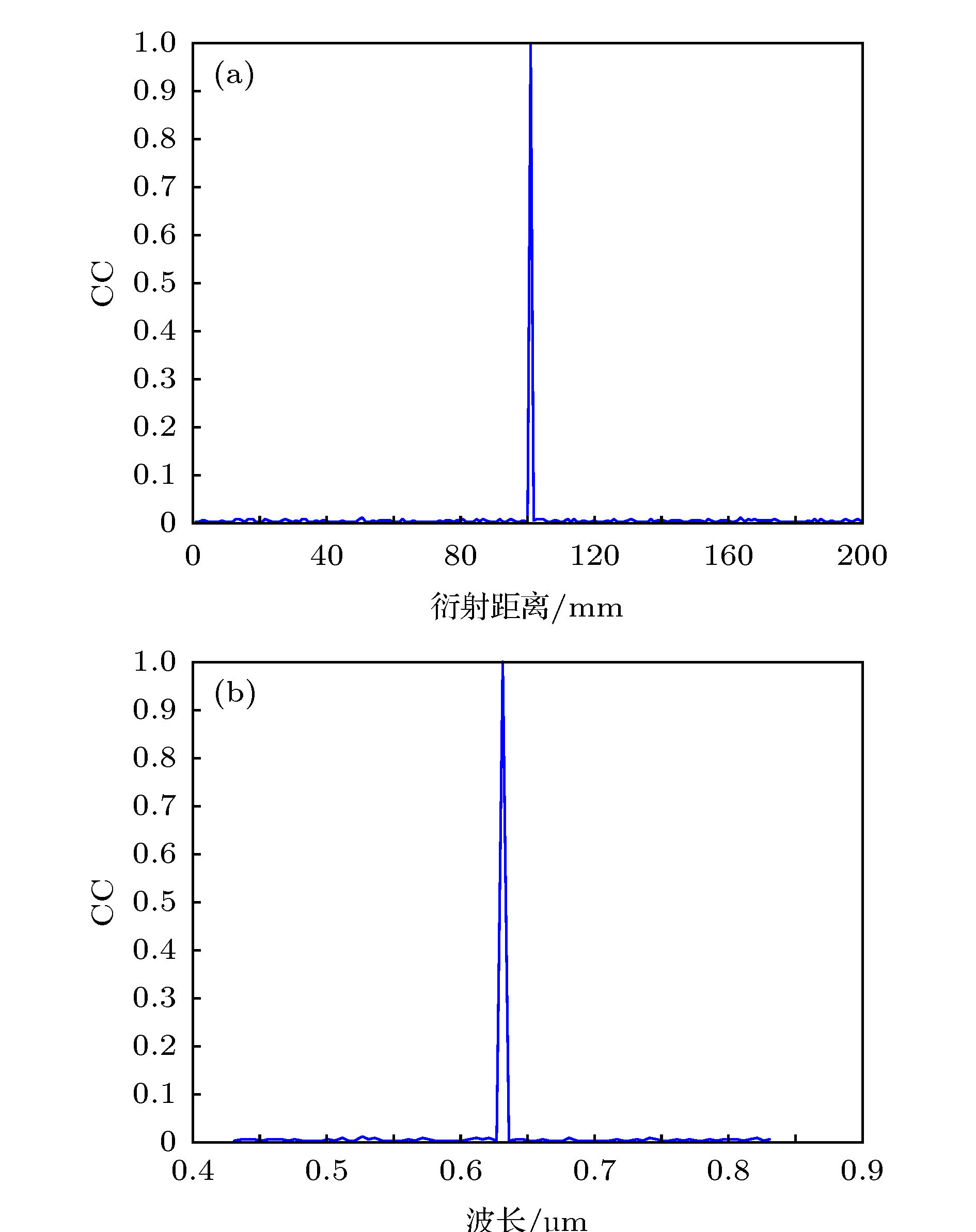
图 11 解密时衍射距离和波长对解密图像的影响, 正确的衍射距离为100 mm(两次衍射距离相同), 正确的波长为0.632 μm (a)衍射距离对解密图像的影响; (b)波长对解密图像的影响
Fig. 11. The effect of diffraction distance and wavelength on decrypted image during decryption: (a) The effect of diffraction distance on the decrypted image; (b) the effect of wavelength on decrypted image. The correct diffraction distance is 100 mm (the two diffraction distances are the same), and the correct wavelength is 0.632 μm.
-
[1] Refregier P, Javidi B 1995 Opt. Lett. 20 767
 Google Scholar
Google Scholar
[2] Tajahuerce E, Javidi B 2001 Appl. Opt. 39 6595
[3] Javidi B 2000 Opt. Eng. 39 2031
 Google Scholar
Google Scholar
[4] Wu C H, Chang J, Quan C G, Zhang Y J 2020 Opt. Commun. 462 125347
 Google Scholar
Google Scholar
[5] Yu H H, Chang J, Liu X, Wu C H, He Y F, Zhang Y J 2017 Opt. Express 25 8860
 Google Scholar
Google Scholar
[6] Sui L S, Gao B 2013 Opt. Laser Technol. 48 117
 Google Scholar
Google Scholar
[7] He W Q, Peng X, Meng X F 2012 J. Opt. 14 075401
 Google Scholar
Google Scholar
[8] Unnikrishnan G, Joseph J, Singh K 2000 Opt. Lett. 25 887
 Google Scholar
Google Scholar
[9] Situ G H, Zhang J J 2004 Opt. Lett. 29 1854
[10] Unnikrishnan G 2000 Opt. Eng. 39 2853
 Google Scholar
Google Scholar
[11] 彭翔, 汤红乔, 田劲东 2007 物理学报 56 2629
 Google Scholar
Google Scholar
Peng X, Tang H Q, Tian J D 2007 Acta Phys. Sin. 56 2629
 Google Scholar
Google Scholar
[12] Peng X, Zhang P, Wei H Z, Yu B 2006 Opt. Lett. 31 1044
 Google Scholar
Google Scholar
[13] Wu C H, Chang J, Xu X X, Zhang Y J 2019 Opt. Commun. 450 87
 Google Scholar
Google Scholar
[14] Shi Y S, Situ G H, Zhang J J 2007 Opt. Lett. 32 1914
 Google Scholar
Google Scholar
[15] QinY, GongQ, WangZ P 2014 Opt. Express 22 21790
 Google Scholar
Google Scholar
[16] Sun M J, Shi J H, Li H, Zeng G H 2013 Opt. Express 21 19395
 Google Scholar
Google Scholar
[17] Chen L F, Chang G J, He B Y, Mao H D, Zhao D M 2017 Opt. Laser Eng. 88 221
 Google Scholar
Google Scholar
[18] Xiang T, Wong K W, Liao X 2007 Chaos (Woodbury, N.Y.) 17 23115
 Google Scholar
Google Scholar
[19] Taneja N, Raman B, Gupta I 2011 Aeu Int. J. Electron. Commun. 65 338
 Google Scholar
Google Scholar
[20] Bhatnagar G, Wu Q M J 2012 Digit. Signal Process. 22 648
 Google Scholar
Google Scholar
[21] 孔德照, 沈学举, 林超, 杨鹏, 潘宇 2013 光学仪器 35 17
 Google Scholar
Google Scholar
Kong D Z, Shen X J, Lin C, Yang P, Pan Y 2013 Opt. Instr. 35 17
 Google Scholar
Google Scholar
[22] 肖宁, 李爱军 2017 应用光学 38 406
Xiao N, Li A J 2017 J. Appl. Opt. 38 406
[23] 彭翔, 位恒政, 张鹏 2007 物理学报 56 3924
 Google Scholar
Google Scholar
Peng X, Wei Z H, Zhang P 2007 Acta Phys. Sin. 56 3924
 Google Scholar
Google Scholar
[24] 史祎诗, 司徒国海, 张静娟 2008 光子学报 37 1779
Shi Y S, Situ G H, Zhang J J 2008 Acta Photon. Sin. 37 1779
计量
- 文章访问数: 8758
- PDF下载量: 98
- 被引次数: 0













 下载:
下载: