-
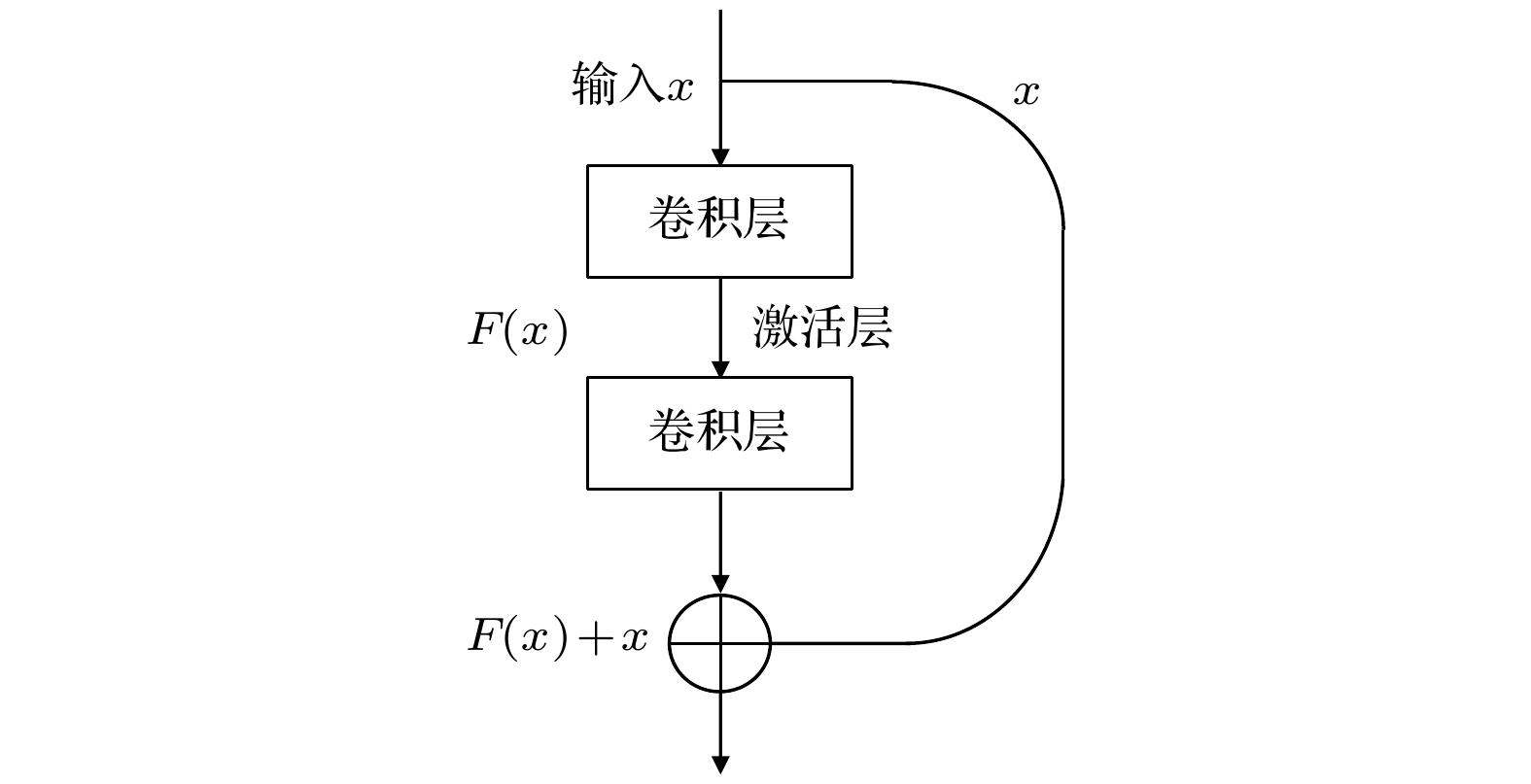
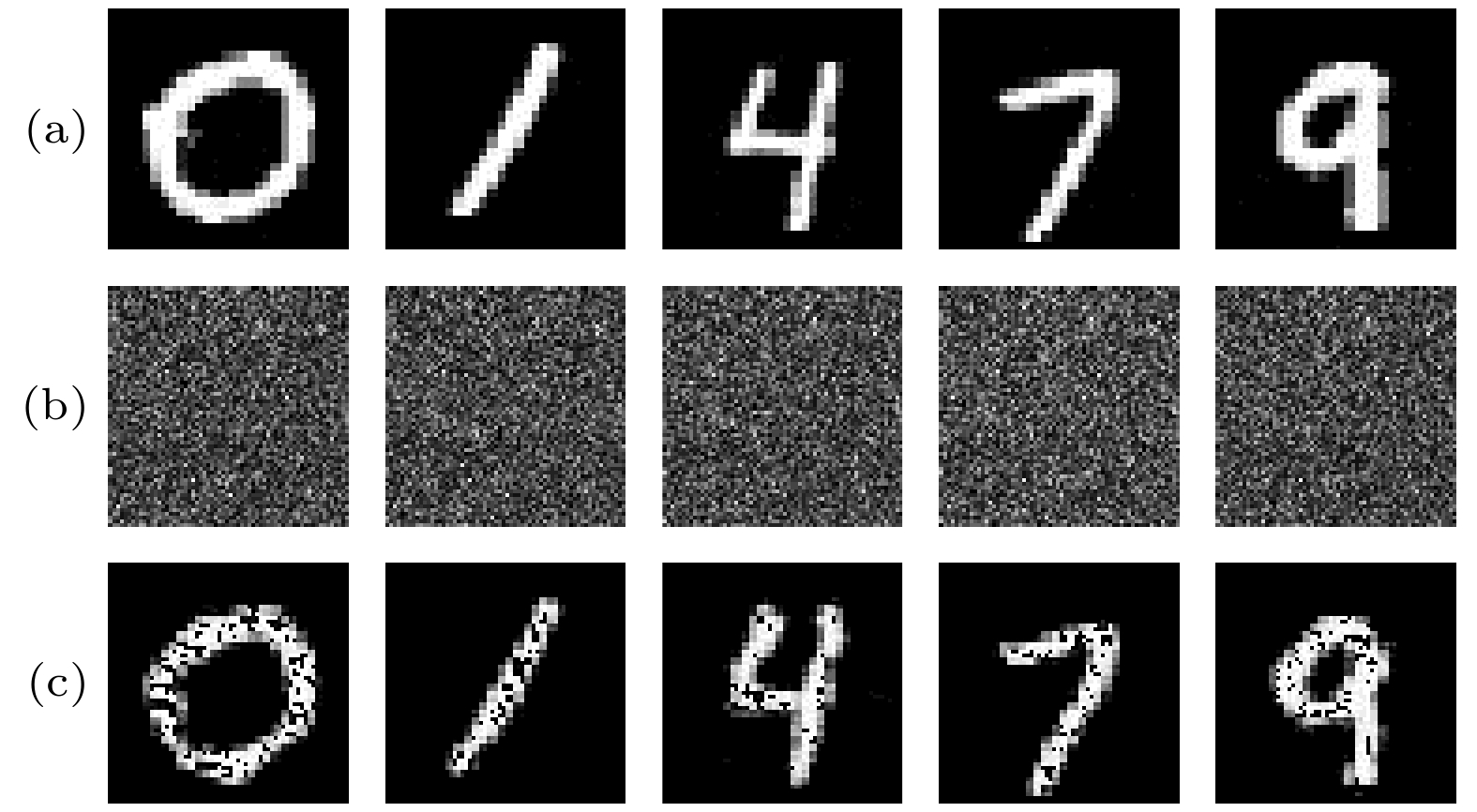
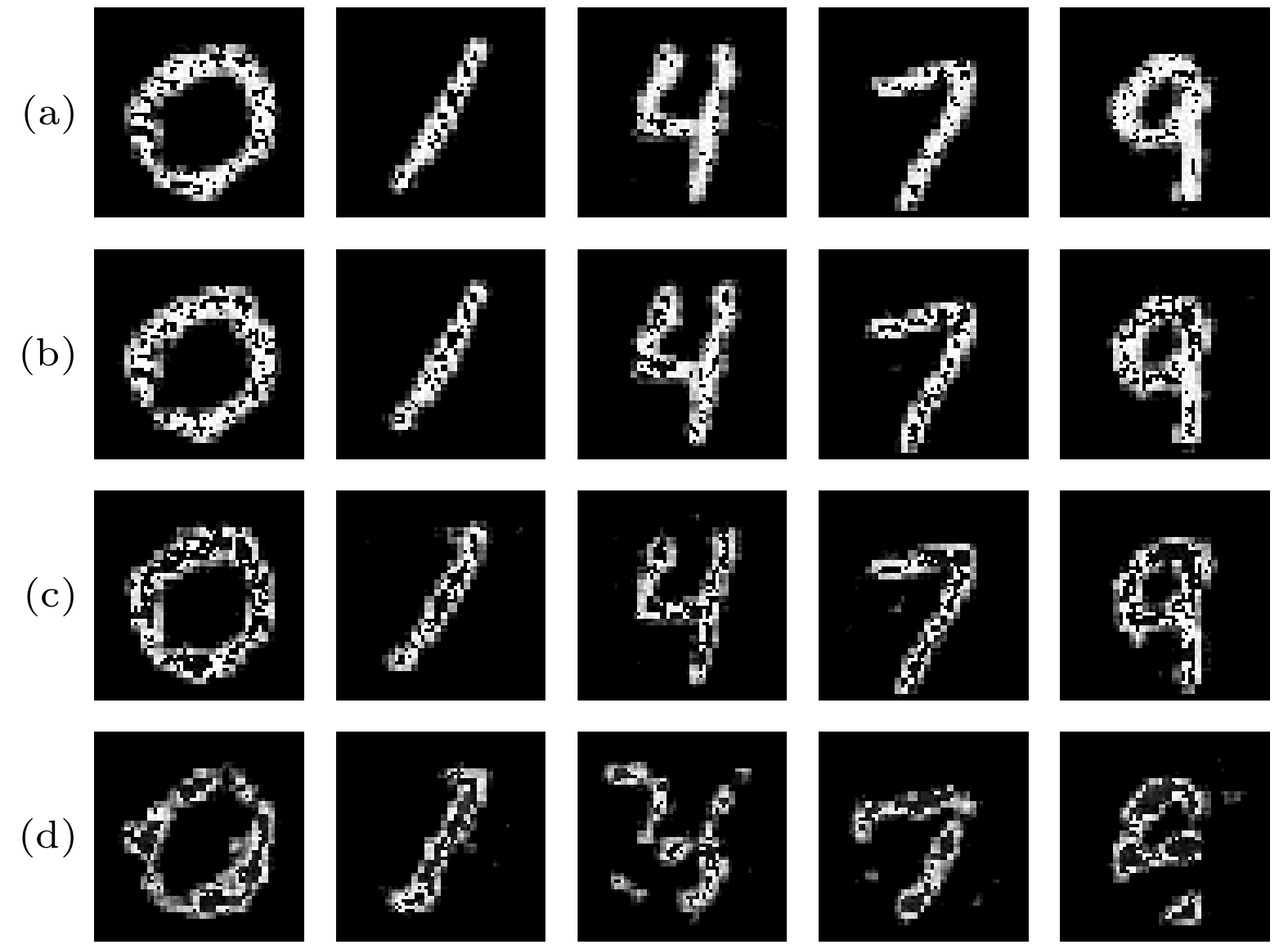
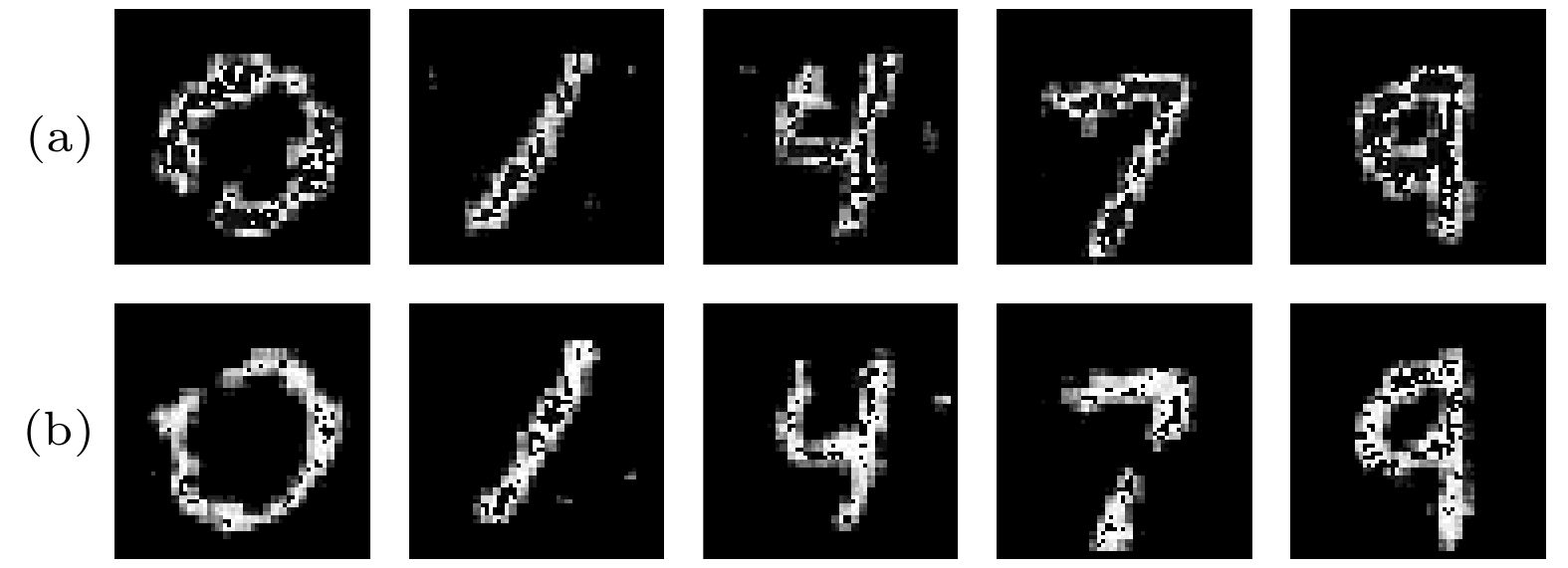
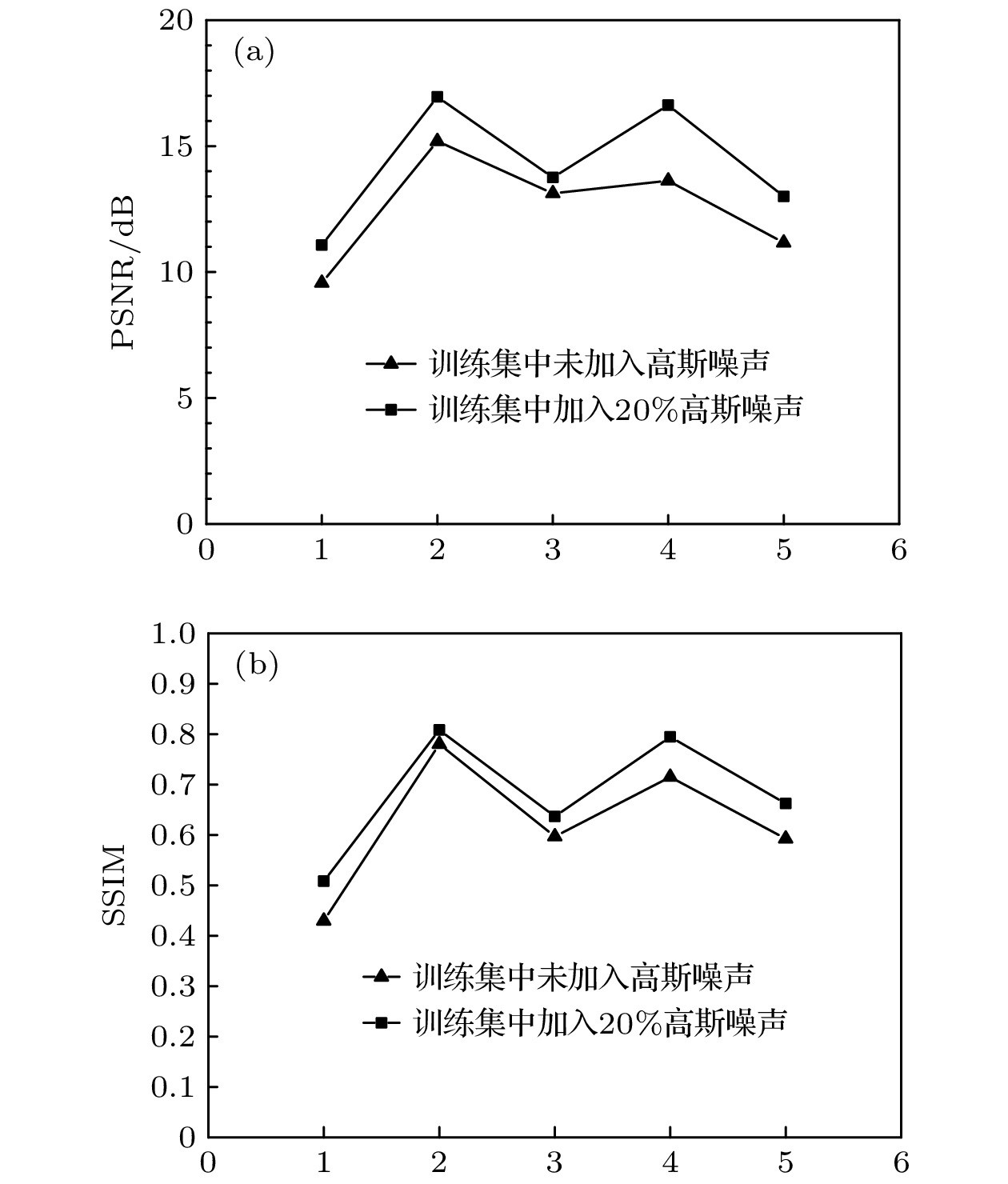
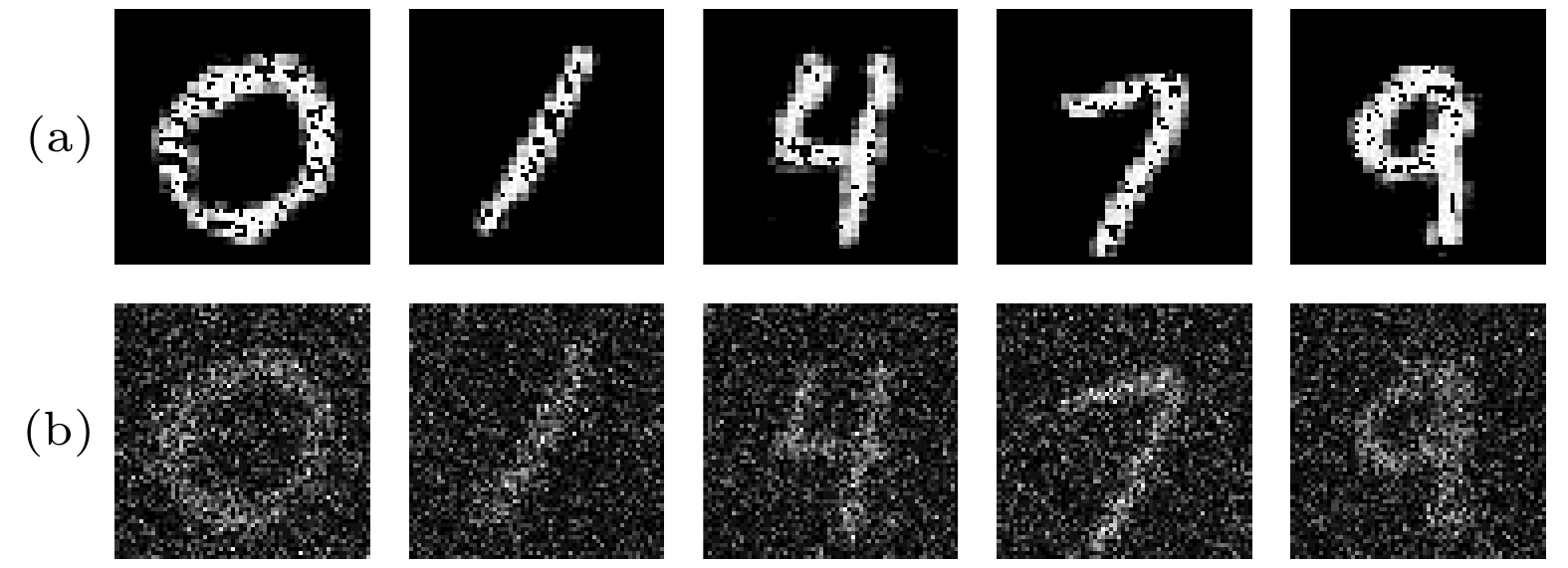
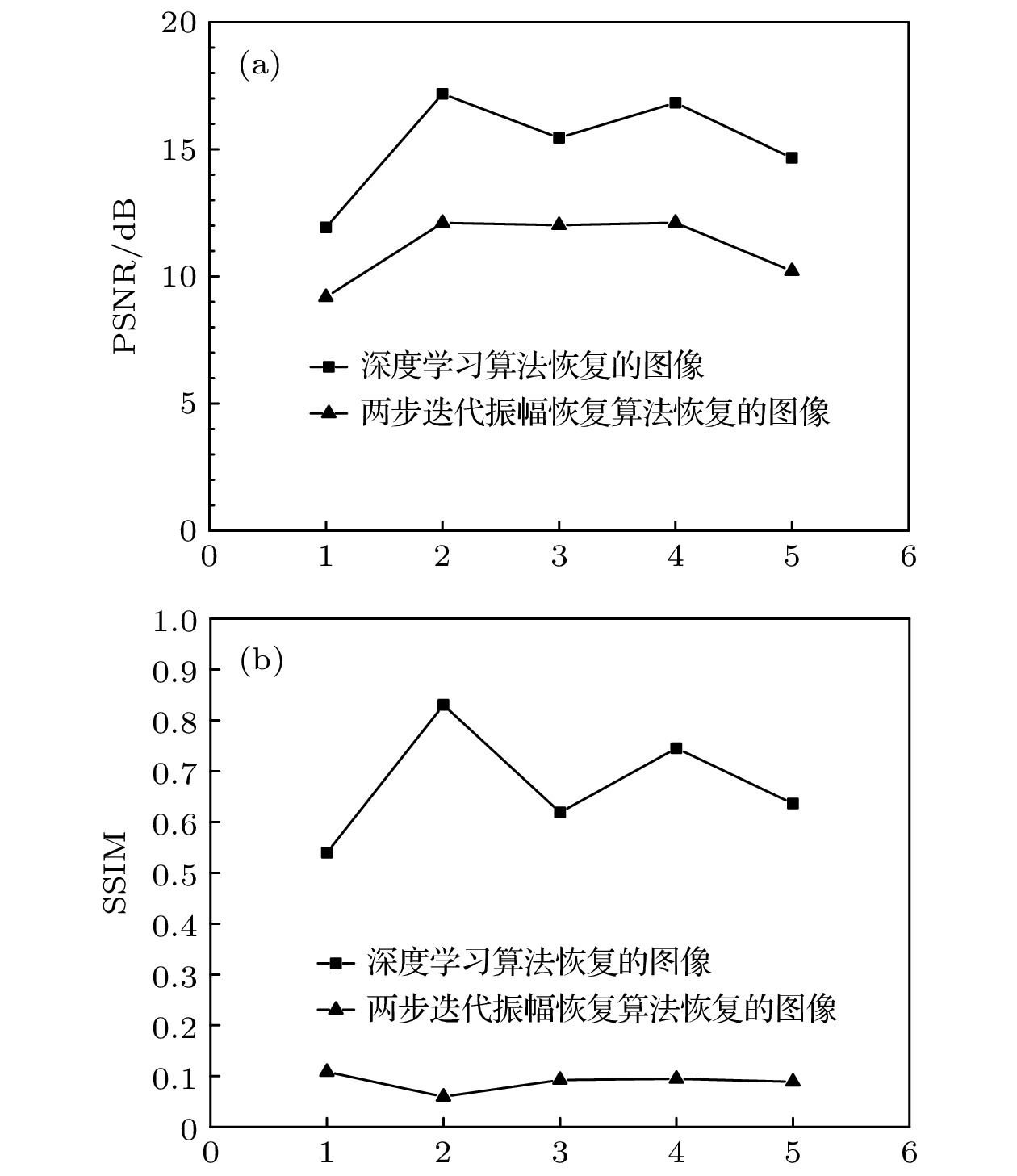
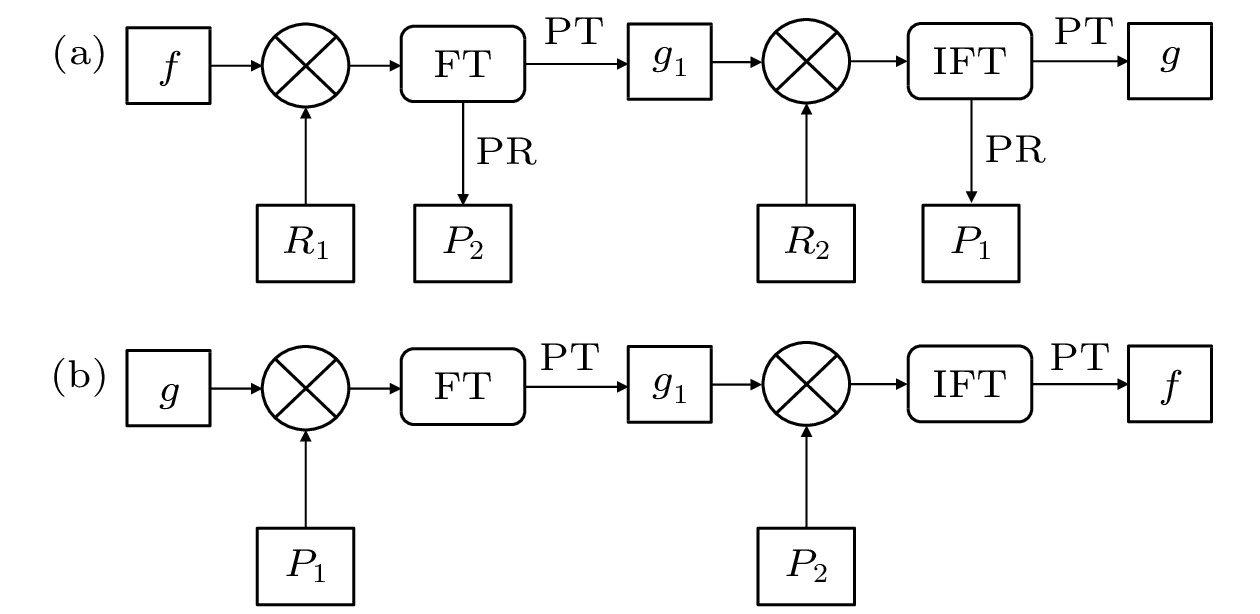
大多数光学加密系统都是对称加密系统, 在光学图像加密中明文和密文之间具有线性关系, 其系统的安全性有待加强. 而基于相位截断傅里叶变换(phase-truncated Fourier transform, PTFT)的非对称加密系统, 其非线性的相位截断操作使加密系统的安全性得到了极大提升. 本文提出使用深度学习方法攻击PTFT加密系统, 通过PTFT加密系统构造出明密文对图像数据集, 然后将其输入残差网络(residual network, ResNet)中进行训练, ResNet自动学习该加密系统的解密特性. 最后应用测试集对训练好的模型进行解密性能测试, 数据表明该模型能够较好地恢复图像并且该模型具有一定的抗噪声能力. 与两步迭代振幅恢复算法相比, 本文所提出方法恢复的图像质量更好.Most of optical encryption systems are symmetric cryptosystems. The plaintext and the ciphertext in optical image encryption are related linearly. The security of the system needs to be strengthened. The asymmetric cryptosystem based on phase truncated Fourier transforms (PTFT) makes the security of the encryption system greatly improved by its nonlinear phase truncation. Deep learning (DL) as a method of machine learning was proposed decades ago. With the development of computer’s performance, the practicality of deep learning proves to be more and more obvious. Recently, deep learning has been effectively used in many fields such as biomedicine, object detection, etc. The good results have been achieved. In this article proposed is the attack to the PTFT encryption system by deep learning. Through the PTFT encryption system, we construct a plaintext-ciphertext paired image dataset and then train it by residual network (ResNet). There are two problems encountered by the traditional neural network model. One is vanishing or named exploding gradient, which makes training effect difficult to converge and the other is a degradation phenomenon. When continuing to increase the number of layers for a suitable depth model, the model accuracy will decline which is not caused by overfitting. This problem can be solved by the ResNet to a certain extent by directly bypassing and then taking the input information to the output to protect the integrity of the information. The biggest difference between ordinary directly connected convolutional neural networks and ResNet is that the ResNet has many bypass branches that directly connect the input to the subsequent layers, so that the subsequent layers can directly learn the residuals. The ResNet can automatically learn the decryption characteristics of the encryption system. Finally, the test set is used to test the decryption performance of the trained model. The data show that the model can restore the image with high quality and the model has a certain anti-noise ability. Compared with the two-step iterative amplitude recovery algorithm, the the method proposed in this paper can recover high quality image.
-
Keywords:
- optical encryption /
- phase truncated Fourier transforms /
- deep learning /
- residual network
[1] Refregier P, Javidi B 1995 Opt. Lett. 20 767
 Google Scholar
Google Scholar
[2] Qin W, Peng X 2010 Opt. Lett. 35 118
 Google Scholar
Google Scholar
[3] Lecun Y, Bottou L, Bengio Y, Haffner P 1998 Proc. IEEE. 86 2278
 Google Scholar
Google Scholar
[4] Krizhevsky A, Sutskever I, Hinton G 2017 Commun. ACM. 60 84
 Google Scholar
Google Scholar
[5] Simonyan K, Zisserman A 2014 arXiv e-prints arXiv: 1409.1556
[6] Szegedy C, Liu W, Jia Y, Sermanet P, Reed S, Anguelov D, Erhan D, Vanhoucke V, Rabinovich A 2015 2015 IEEE Conference on Computer Vision and Pattern Recognition (CVPR) Boston, USA, June 7−12, 2015 p1
[7] He K, Zhang X, Ren S, Sun J 2015 arXiv e-prints arXiv: 1512.03385
[8] Hai H, Pan S, Liao M, Lu D, He W, Peng X 2019 Opt. Express 27 21204
 Google Scholar
Google Scholar
[9] Srivastava R, Greff K, Schmidhuber J 2015 Proceedings of the 28th International Conference on Neural Information Processing Systems Montreal, Canada, December 7−10, 2015 p2377
[10] Drozdzal M, Vorontsov E, Chartrand G, Kadoury S, Pal C 2016 arXiv e-prints arXiv: 1608.04117
[11] Glorot X, Bordes A, Bengio Y 2011 Proceedings of the 14th International Conference on Artificial Intelligence and Statistics (AISTATS) Fort Lauderdale, USA, April 11−13, 2011 p315
[12] Nair V, Hinton G 2010 Proceedings of the 27th International Conference on International Conference on Machine Learning Madison, USA, June 21−24, 2010 p807
[13] Ioffe S, Szegedy C 2015 Proceedings of the 32nd International Conference on International Conference on Machine Learning Lille, France, July 6−11, 2015 p448
[14] Dong C, Loy C C, He K, Tang X 2014 Proceedings of the 13th European Conference on Computer Vision Zurich, Switzerland, September 6−12, 2014 p184
[15] Ishikawa M 1996 Neural Networks. 9 509
 Google Scholar
Google Scholar
[16] Ciregan D, Meier U, Schmidhuber J 2012 2012 IEEE Conference on Computer Vision and Pattern Recognition Providence, USA, June 16−21, 2012 p3642
[17] Kingma D P, Ba J 2014 arXiv e-prints arXiv: 1412.6980
[18] Horé A, Ziou D 2010 20th International Conference on Pattern Recognition Istanbul, Turkey, Auguest 23−26, 2010 p2366
[19] Wang Z, Bovik A C, Sheikh H R, Simoncelli E P 2004 IEEE Trans. Image Process. 13 600
 Google Scholar
Google Scholar
[20] Wang X, Zhao D 2012 Opt. Commun. 285 1078
 Google Scholar
Google Scholar
-
-
[1] Refregier P, Javidi B 1995 Opt. Lett. 20 767
 Google Scholar
Google Scholar
[2] Qin W, Peng X 2010 Opt. Lett. 35 118
 Google Scholar
Google Scholar
[3] Lecun Y, Bottou L, Bengio Y, Haffner P 1998 Proc. IEEE. 86 2278
 Google Scholar
Google Scholar
[4] Krizhevsky A, Sutskever I, Hinton G 2017 Commun. ACM. 60 84
 Google Scholar
Google Scholar
[5] Simonyan K, Zisserman A 2014 arXiv e-prints arXiv: 1409.1556
[6] Szegedy C, Liu W, Jia Y, Sermanet P, Reed S, Anguelov D, Erhan D, Vanhoucke V, Rabinovich A 2015 2015 IEEE Conference on Computer Vision and Pattern Recognition (CVPR) Boston, USA, June 7−12, 2015 p1
[7] He K, Zhang X, Ren S, Sun J 2015 arXiv e-prints arXiv: 1512.03385
[8] Hai H, Pan S, Liao M, Lu D, He W, Peng X 2019 Opt. Express 27 21204
 Google Scholar
Google Scholar
[9] Srivastava R, Greff K, Schmidhuber J 2015 Proceedings of the 28th International Conference on Neural Information Processing Systems Montreal, Canada, December 7−10, 2015 p2377
[10] Drozdzal M, Vorontsov E, Chartrand G, Kadoury S, Pal C 2016 arXiv e-prints arXiv: 1608.04117
[11] Glorot X, Bordes A, Bengio Y 2011 Proceedings of the 14th International Conference on Artificial Intelligence and Statistics (AISTATS) Fort Lauderdale, USA, April 11−13, 2011 p315
[12] Nair V, Hinton G 2010 Proceedings of the 27th International Conference on International Conference on Machine Learning Madison, USA, June 21−24, 2010 p807
[13] Ioffe S, Szegedy C 2015 Proceedings of the 32nd International Conference on International Conference on Machine Learning Lille, France, July 6−11, 2015 p448
[14] Dong C, Loy C C, He K, Tang X 2014 Proceedings of the 13th European Conference on Computer Vision Zurich, Switzerland, September 6−12, 2014 p184
[15] Ishikawa M 1996 Neural Networks. 9 509
 Google Scholar
Google Scholar
[16] Ciregan D, Meier U, Schmidhuber J 2012 2012 IEEE Conference on Computer Vision and Pattern Recognition Providence, USA, June 16−21, 2012 p3642
[17] Kingma D P, Ba J 2014 arXiv e-prints arXiv: 1412.6980
[18] Horé A, Ziou D 2010 20th International Conference on Pattern Recognition Istanbul, Turkey, Auguest 23−26, 2010 p2366
[19] Wang Z, Bovik A C, Sheikh H R, Simoncelli E P 2004 IEEE Trans. Image Process. 13 600
 Google Scholar
Google Scholar
[20] Wang X, Zhao D 2012 Opt. Commun. 285 1078
 Google Scholar
Google Scholar
计量
- 文章访问数: 8961
- PDF下载量: 132
- 被引次数: 0












 下载:
下载: